There are ample options in profiles in salesforce. In this post I will discuss about different options with which you can secure data (only, not all options) from different users.
With OWD, you can decide who can view, edit the record and who cannot. I will try to explain you how profiles can be helpful in sharing records and its permission.
But first let’s see how you can reach profiles.
Step 1: Login into your Salesforce Org.
Step 2: In Quick Search type “Profiles”, Select Profiles option.
You will see list of all profiles that are available in System. Both Standard profiles and Custom profiles.

Here you can see a column named Custom, you can differentiate between Standard and Custom by the checkbox field. If check box is unchecked, its standard profile and if check box is checked, its custom profile.
There are limited standard profiles, predefined by salesforce. You can create custom profiles and assign permission as per business requirement. In this post we will only discuss about different options to secure data.
To secure data through profiles there are multiple options.
- Object Permission
- Field-Level Security
Object Permission.
Object permissions specify the base-level access users can have to create, read, edit, and delete records for each object. You can manage object permissions in permission sets and profiles.
You can assign Read, Create, Edit, Delete, View All, Modify All permissions in Object permission. Through profiles, object permissions either respected or override sharing rules and settings (OWD access).
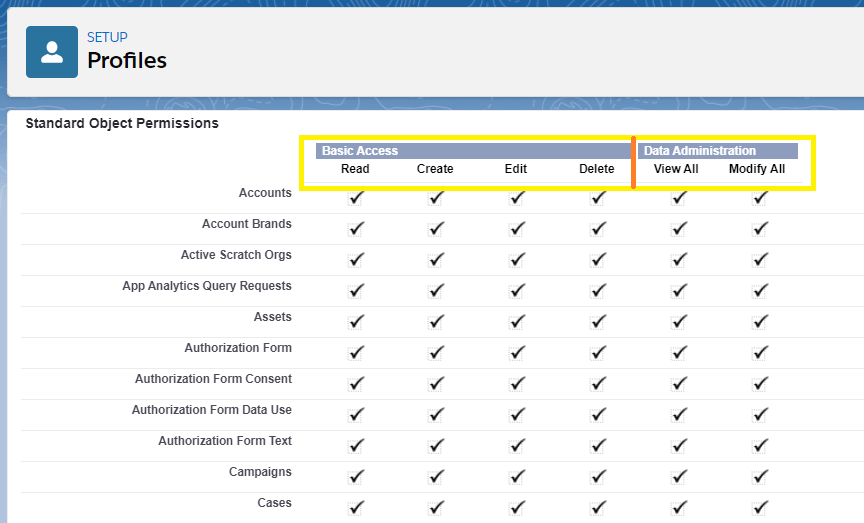
| Permission | Description | Respect/Override |
|---|---|---|
| Read | User can view records | Sharing is respected |
| Create | User can read and create records | Sharing is respected |
| Edit | User can read and edit records | Sharing is respected |
| Delete | User can read and edit records but can delete only records that he owns. | Sharing is respected |
| View All | User can view all records irrespective of OWD access. | Sharing is overridden |
| Modify All | User can view,edit and delete all records irrespective of OWD access. | Sharing is overridden |
Note: In simple terms you can consider profiles as enabling buttons for different operations like,
if user is given Create permission, then user can see “New” button when he clicks on object tab.
If, user is given edit permission and not create, then user can see edit button in record, but not new button and so on.
View All and Modify All overrides and gives all permissions including delete permission.
“Modify All” on documents allows access to all shared and public folders, but not the ability to edit folder properties or create new folders. To edit folder properties and create new folders, users must have the “Manage Public Documents” permission.
Field-Level Security.
There are lots of users in salesforce and records can be shared with multiple users. There can be a scenario where some fields should be restricted for a specific profile. Field-level security settings let you restrict users’ access to view and edit specific fields.
You can access field level security in profiles. Once you open a profile, scroll down to Field-Level Security. Here you can need to click on view link against the object where you want to set Field-Level Security. (I will show field level security of Account).
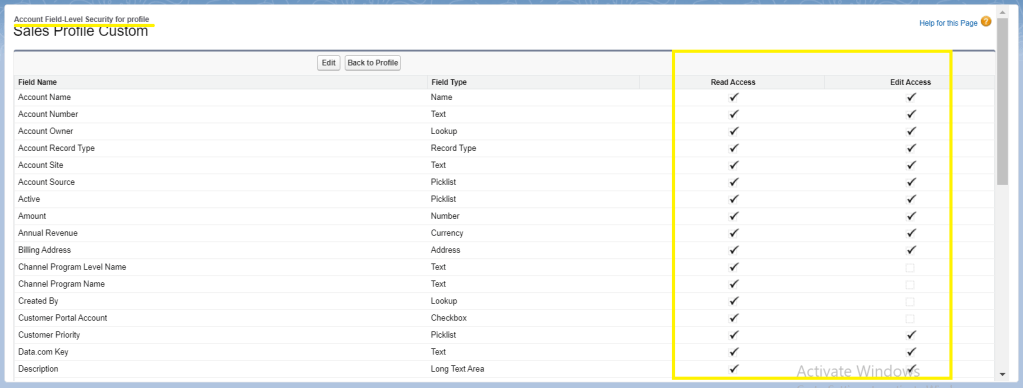
Here once you click on Edit button on top, you can give Read access and Edit access to the profile as per business requirement.
You can restrict user access in:
- Detail and edit pages
- Related lists
- List views
- Reports
- Connect Offline
- Email and mail merge templates
- Custom links
- The partner portal
- The Salesforce Customer Portal
- Synchronized data
- Imported data
Page layouts and field-level security settings determine which fields a user sees. The most restrictive field access settings of the two always applies.
Resources
